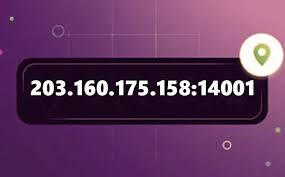
Introduction What Is 203.160.175.158.14001?
When it comes to internet protocols and network security understanding how IP addresses work can be a key element in optimizing performance. One such address 203.160.175.158.14001 may appear confusing at first glance but with a closer look it can reveal important information about network configurations and security.
This article will explore the details behind this specific IP address helping you understand its role how it works and how you can ensure the best performance and security for your network.
Understanding the Basics of IP Addresses
Before diving deep into 203.160.175.158.14001 it’s important to first understand what an IP address is and how it functions in a network. An IP (Internet Protocol) address is a unique identifier for devices on a network whether it’s a computer smartphone or server. It allows devices to communicate with each other over the internet.
There are two types of IP addresses
- IPv4 The most common form consisting of four sets of numbers separated by dots (e.g. 192.168.1.1).
- IPv6 A newer version designed to solve the problem of IPv4 address exhaustion.
The IP address 203.160.175.158.14001 may seem like a standard address but it’s actually an example of a non-standard format which brings up questions about how it’s structured and why it’s significant.
How Does 203.160.175.158.14001 Work?
Now that we understand the basics let’s break down 203.160.175.158.14001 into its components. The “203.160.175.158” part follows the typical IPv4 format but the “.14001” is unusual. This additional number is often used for specific types of communication such as ports or services associated with the address.
Each IP address is associated with specific services or applications and these services are often identified by ports. A port number allows the operating system to route traffic to the right application. For example port 80 is typically used for HTTP traffic while port 443 is used for HTTPS.
The number 14001 could represent a custom service or a specific configuration that requires a unique port.
Why Is 203.160.175.158.14001 Important for Network Security?
Network security is critical for businesses and individuals alike and understanding the implications of an IP address like 203.160.175.158.14001 can help improve your security posture. If you’re an IT professional or someone concerned with network performance you should be aware of any unusual or non-standard formats in your system.
Addresses with non-standard formats (such as ports in unusual places) could indicate
- Potential security risks Malicious traffic often uses non-standard configurations to bypass conventional security protocols.
- Custom configurations Some applications may use unique port numbers for their services requiring special attention for security.
How to Monitor and Secure IP Addresses Like 203.160.175.158.14001
- Monitor Network Traffic Use network monitoring tools to keep track of any unusual activity related to specific IP addresses and ports.
- Use Firewalls Set up a firewall to block any unwanted traffic particularly if you notice suspicious or non-standard port usage.
- Regular Updates Ensure that your system and software are up-to-date with the latest security patches.
Learn more about securing IPs and networks here
Conclusion
Understanding IP addresses especially those with non-standard configurations like 203.160.175.158.14001 is crucial for maintaining a secure and efficient network. By monitoring network traffic using firewalls and keeping systems updated you can ensure your network stays safe from potential threats.
For those looking to dive deeper into network security be sure to explore more resources and tools available online to strengthen your understanding.
FAQs
- What is an IP address?
- An IP address is a unique identifier for a device on a network allowing communication over the internet.
- Why does 203.160.175.158.14001 have an unusual format?
- The “.14001” likely represents a port number which identifies a specific service or application associated with the IP address.
- How can I monitor unusual IP addresses?
- Use network monitoring tools that track incoming and outgoing traffic to detect unusual activity.
- Can I block specific IP addresses?
- Yes you can block specific IP addresses using firewalls to protect your network from unwanted traffic.
- What is the difference between IPv4 and IPv6?
- IPv4 is the most common format while IPv6 is the newer version designed to accommodate more addresses.
- How does a firewall help with network security?
- A firewall monitors and controls incoming and outgoing network traffic helping block malicious connections.
- What are the risks of non-standard port usage?
- Malicious actors often use non-standard ports to bypass security measures making it harder to detect malicious traffic.
- Why should I update my software regularly?
- Regular updates ensure that any security vulnerabilities are patched reducing the risk of exploitation.